Developing a New Native Ads Dashboard Using Server-Driven UI

-
Humad Syed, Software Engineer
- Feb 15, 2022
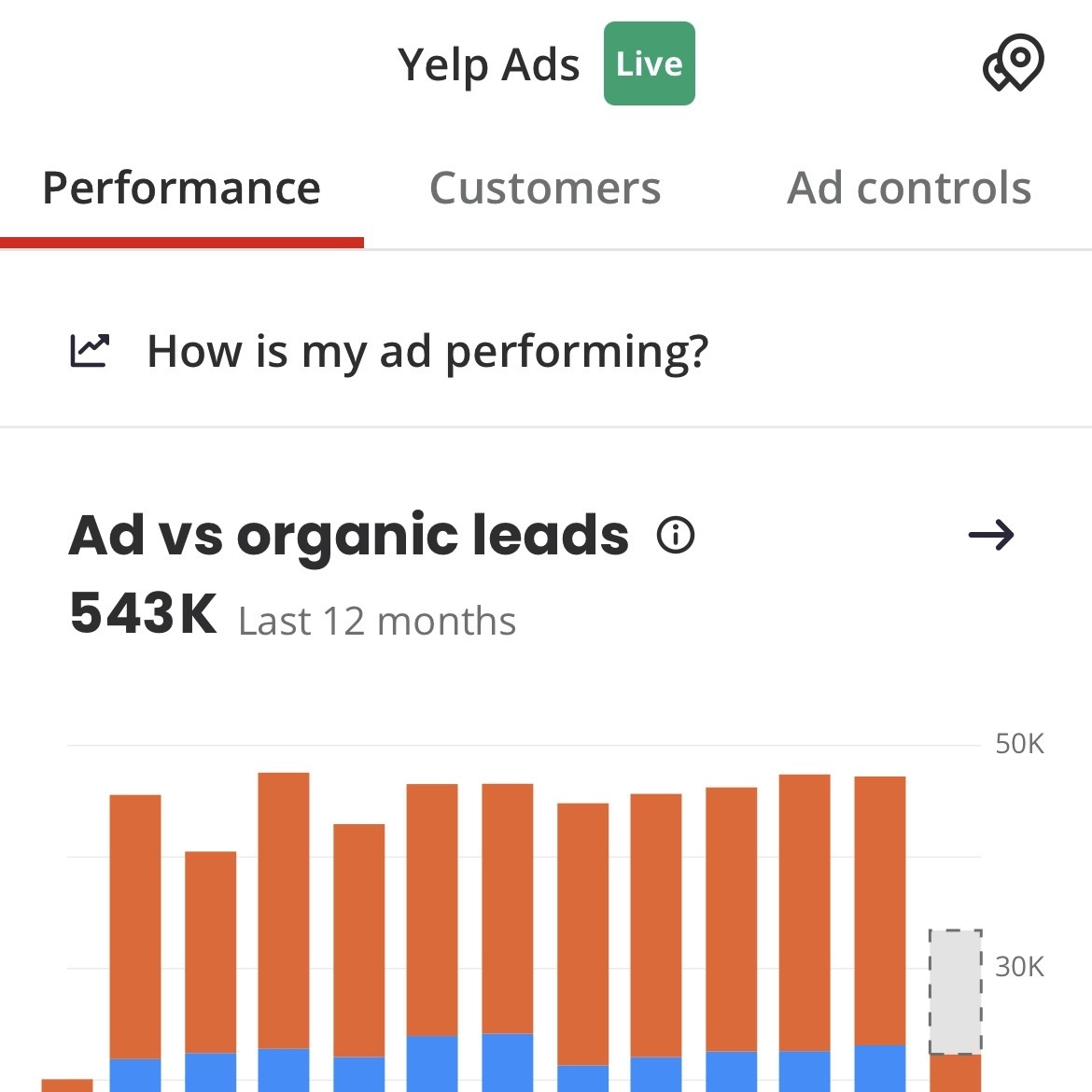
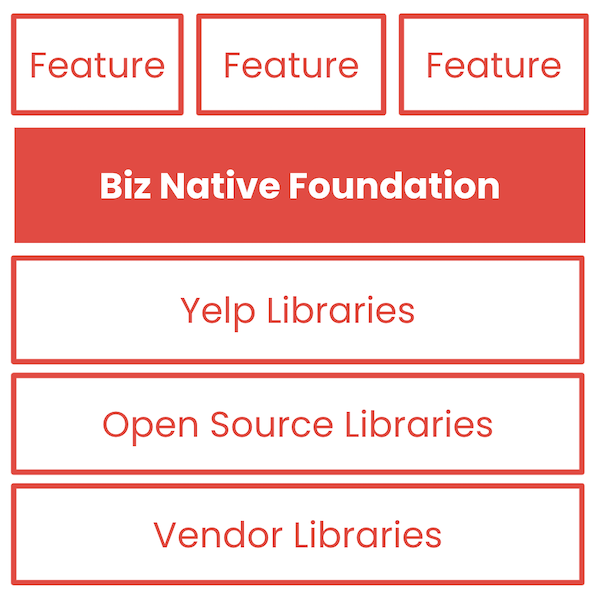
Updating the ads experience for Yelp Advertisers by creating a new Native Ads Dashboard using Server-Driven UI. What is the Ads Dashboard? The Yelp Ads Dashboard is a tool that advertisers can use to update their ad settings and keep track of how their ad is performing. In 2020, we revamped the Ads Dashboard web experience to provide greater visibility into an ad’s performance and better access to control and customize options from a single page. Ads Dashboard on Desktop Recreating the Experience on Mobile In order to ensure consistency across platforms from both a visual and feature standpoint, we...